Latest
03
Mar
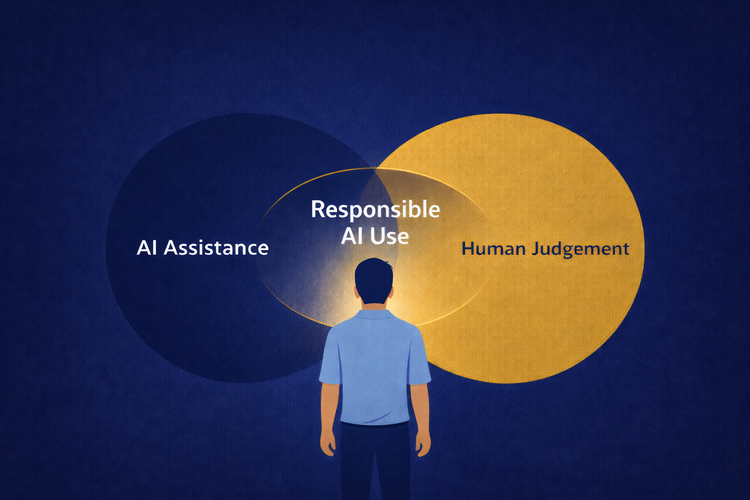
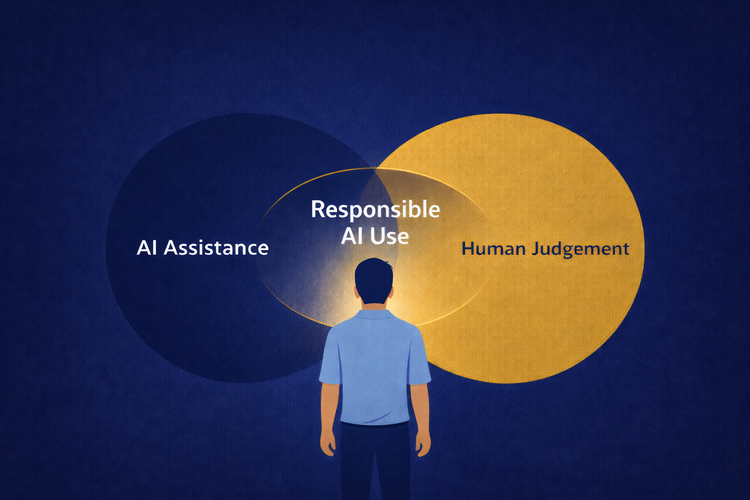
AI and the Human Responsibility That Comes With It
AI speeds up our work, but convenience should never replace care. Human habits and judgment remain the strongest defense in the age of AI.
3 min read
04
Feb

Your Data’s Everywhere. Here’s How to Take It Back.
Digital clutter creates risk. A few intentional habits can help you organize your data and protect what matters.
3 min read
30
Jan

Why Process Shapes Security Culture
Effective process does more than guide actions. It influences how people think about security.
2 min read
08
Dec

The Real Cost of Free Wi-Fi
Free Wi-Fi feels harmless, but it can expose more than you realise. Here’s what actually happens on open networks and what you can do to keep your information safe.
3 min read
30
Oct

Awareness Starts With You: Small Habits, Big Security Wins
Security requires daily action and personal ownership. It's built on quiet, consistent choices.
2 min read
27
Aug

Your Data: The Fuss and Why You Should Care
Every tap, scroll, and 'Allow All' is a quiet transaction. The price is your data, but your choices don't have to be blind.
3 min read
30
Jul

Strong Security Starts on Paper
Documentation isn’t extra — it’s the first part of doing it right.
3 min read
17
Jul
Beyond ‘Accept All’: What You Need to Know About Website Cookies
They sweeten your online experience — but leave crumbs that follow. Here's what to know about website cookies.
2 min read
08
Jul

Security is Not an Add-On Feature
“Security must be proactive, not reactive — integrated from the start, measured continuously, and adapted as the business evolves.”
2 min read
28
Jun
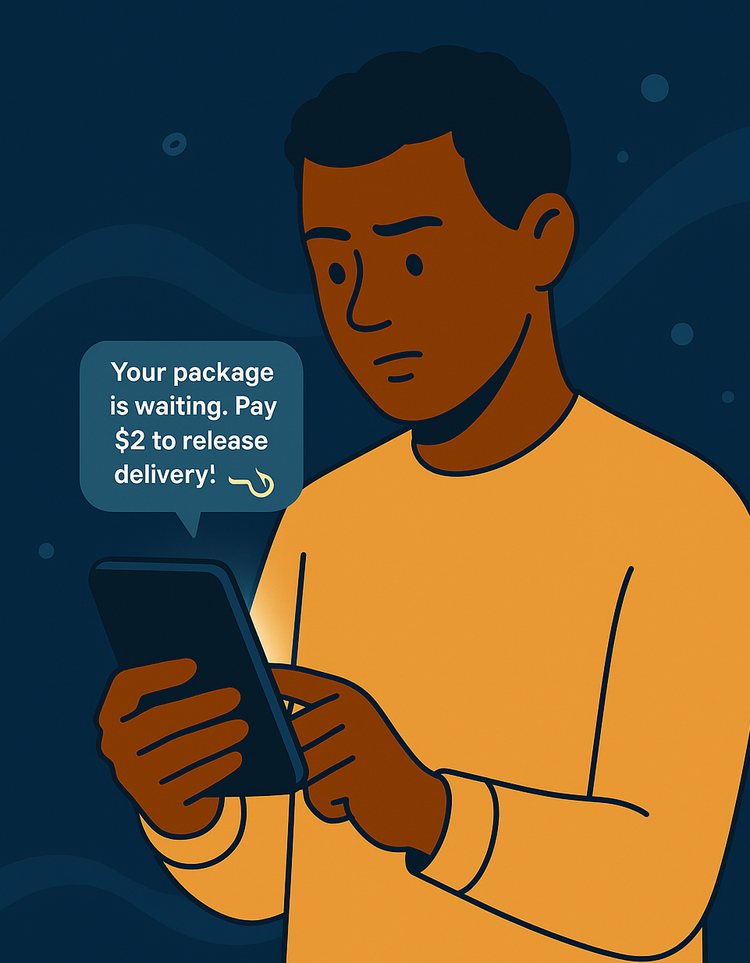
Smishing: When Scams Hit Your Phone
Not every text is safe. Smishing scams look ordinary – here’s how to outsmart them.
2 min read